The “Sign in with Apple” works like the login with Facebook or Google account. It is the method known as Oauth, a way of centralizing entries in an account. One of Apple’s proposals is to make the system more secure and private, by generating a random email address for each registration.

How Oauth works
The platforms (Facebook, Google, Twitter, Linkedin, etc.) provide APIs for developers to implement the login tool on the website or application.
When the user arrives at the site for the first time, instead of filling in the entire registration form with personal information: name, e-mail, date of birth, photo, address and the like; he must confirm his identity from an email sent to that address.
With the login via Facebook, Google or Apple, these platforms already confirm that the information belongs to that user and provide the necessary data for the registration, without the need to type everything again.
Everything happens with explicit authorization from the user, who can still choose what information he wants to share – the mandatory ones are, usually, name, email and profile picture.
Why use Sign in with Apple?
Apple’s claim is that the “Sign in with Apple” tool guarantees user privacy. Since Google and Facebook are companies focused on collecting data to target relevant ads, Apple has no interest in customer data for advertising.
On the other side of the screen, even though the sites have access to the content of the user’s public profile, they can still send requests to Facebook or Google to request more updated information. If the user consents, the data will be shared.

Hidden emails:
Another advantage is that Sign in with Apple allows you to hide the email address used when registering. When logging in to a website with this Apple tool, the user can choose to hide the email (which is the same as the Apple ID), thus generating a random address that forwards to the main one.
This gives the user more control. All of these random emails generated by Apple can be unsubscribed from the Apple ID account page. So, if a database leaks or multiple spam emails start arriving in the inbox, you can find out where they came from to stop access. Without exposing the main email.
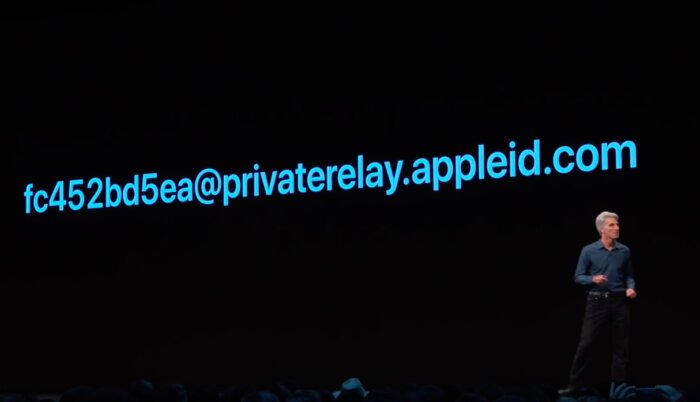
This is an example of a random email generated for a registration
What are the requirements for using Apple login?
- An Apple ID with active two-factor authentication;
- Be with the same iCloud and Apple ID on the device.
It is also possible to use Apple’s login on Windows or Android, as long as the website or app developer has implemented the feature on these systems. If so, a page will open for entering Apple ID credentials.
How to use Sign in with Apple?
Once you are on a website or app with the feature enabled, a button will appear on the login or registration screen.
- Click on “Sign in with Apple”;
- Touch “Continue”;
- Choose whether you want to use your primary email or hide it so that Apple generates an alternate address;
- Authenticate via Face ID, Touch ID or access code.
