The technology Machine-to-machine, or M2M, is a broad label that can be used to describe any technology that allows network devices to exchange information and perform actions without the manual intervention of humans.
It consists of the automated exchange of information between devices such as machines, vehicles or other equipment, both in the industrial and in the private environment. These communicate with one another or with a central location (database), increasingly using the Internet and the various access networks, such as the cellular network.
A common application is the remote monitoring, management, control and maintenance of machines, equipment and systems, which is traditionally called telemetry. M2M technology has linked these information and communication technologies.
M2M solutions streamline almost every industry workflow, and result in productivity gains.
In addition, M2M technology reduces downtime. An example is the automotive industry. Used parts are reported through an e-Kanban system to the supplier. This, therefore, recognizes the necessary parts and quantities.
Subsequent rationalization of business processes and consequent cost reduction mean that the industry – and also the company – has great market potential.
History of M2M technology
The roots of M2M are firmly planted in the manufacturing industry where other technologies, such as SCADA and remote monitoring, help remotely manage and control equipment data.
The first use of M2M communication is often credited to Theodore Paraskevakos, who invented and patented the technology related to data transmission via telephone lines, the basis for the modern caller ID.
Nokia was one of the first companies to use the acronym in the late 1990s. In 2002 it partnered with Opto 22 to offer M2M wireless communications services to its customers.
In 2003, M2M Magazine was launched. Since then, the publication has defined the six pillars of M2M.
M2M Applications
- Transport
- Fleet Management
- Facilities management
- Supply Companies
- Vending Machines
- Security/alarm/monitoring systems
- Health/Medical
- Production/automation
Basic concept of an M2M application
 What is M2M communication? (Machine to Machine)
What is M2M communication? (Machine to Machine)
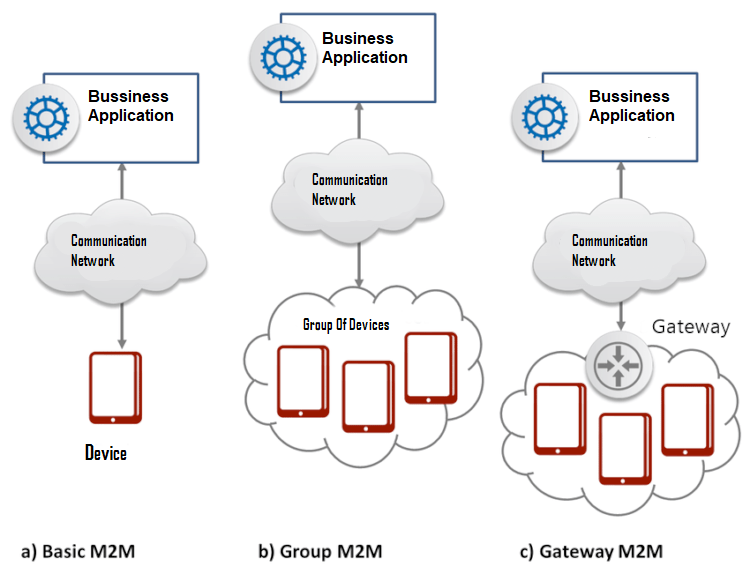
M2M systems are mainly characterized by three basic components:
1. Endpoint of data (EndPoint Data = DEP). Such as a vending machine to be monitored.
2. Communication Networks:
- Mobile, for example, GSM, SMS, GPRS, EDGE, UMTS, HSPA, HSDPA, LTE
- Wired, for example, fixed lines, ISDN, DSL, Ethernet (LAN)
- Wireless systems such as Bluetooth, RFID (active/passive) ZigBee, satellite radio, data radio or WirelessHART, LoRa.
3. Data Integration Point (DIP), for example, a server that monitors the levels of all vending machines.
The final data collection point (DSEP) is a compact microcomputer controlled system (Data Collector) – a transmitter that is associated with a terminal. Within a closed network, there may be multiple data collection terminals and associated devices or equipment. With the help of the DSEP machines, the exchange takes place through data from a communication network with the data integration point (DIP) – the receiver – of which with a central location (database) is connected.
In a complex network, there may be multiple DIPs. They serve and receive data from their respective designated DSEPs. Thus it can arise at several levels in an M2M application, a pyramid-shaped topology. The information flows not only in the direction of Central. Thus, communication between individual DSEPs is also possible.
The overall data transfer can occur through a mobile network. For example, a device sends an error message directly to a selected group of engineers via SMS.
Components of an M2M solution
M2M solutions are basically defined from several interdependent components that allow communication between machines. These mainly include:
- hardware components such as modems, RFID readers, sensors, switches, industrial PCs, servers, etc.
- Mobile and fixed telephony services
- Integration of systems and consulting services
- Applications such as server applications, “Point to Point” applications.
Success factors of M2M solutions
Close cooperation between solution partners, network operators and customers is the key to the successful planning and implementation of M2M solutions. In addition, the success of an M2M solution also depends on the following factors:
- Value added (cost-benefit analysis → Business Case)
- Company capacity (Acceptance → Privacy)
- Proper hardware (cheap hardware can generate costs higher in circumstances than expensive hardware → total cost of ownership and return on investment)
- Proper communication
- Networks (today increasingly mobile networks → GPRS, EDGE, UMTS, HSPA)
- Prices (in particular mobile tariffs)
- Protocols (the future is IP → wide range of applications and investment protection)
- Complete integration into existing workflows (automation → benefits).
Internet of Things (IoT)
The term Internet of Things (IoT) describes that the PC increasingly disappears as a unit, and is replaced by “intelligent objects”. Instead, to be the object of human attention itself, the role of the “Internet of Things” is to help people imperceptibly in their activities.
Built-in microprocessors, smaller and smaller, should help people without distracting or even perceiving. Thus, for example, the miniaturized computer, called wearables, incorporated with various sensors directly into clothing, smartwatches, smartphones, tablet, PC or similar.
The Internet of Things defines the linking of clearly identifiable physical objects (things) to a virtual representation in a web-like structure. There is no longer participation/action of only human participants, but also of devices/things.
M2M vs. IoT
While many use the terms interchangeably, M2M and IoT are not the same thing. Internet of Things needs M2M, but M2M does not need IoT.
Both terms refer to the communication of connected devices, but M2M systems are often isolated, independent network equipment. IoT systems take M2M to the next level, bringing together disparate systems in a large connected ecosystem.
M2M systems use peer-to-peer communications between machines, sensors, and hardware over wired or wireless networks, while IoT systems rely on IP-based networks to send data collected from IoT devices to gateways, cloud platforms, or middleware.
